
Zero Trust Outcome
Zero Trust is an outcome, not a specific product. Understanding this distinction may be one of the most important things a local government IT leader can do right now.
Guides for navigating IT capabilities and responsibilities.

Zero Trust is an outcome, not a specific product. Understanding this distinction may be one of the most important things a local government IT leader can do right now.
Many organizations take pride in having strong employee handbooks and clear HR policies. But when it comes to cybersecurity policy — a core foundation of business protection — they fall short. This is a dangerous gap.
Cybersecurity policy isn’t just an IT problem. It’s a business risk issue. It affects reputation, compliance, and your ability to recover from incidents. And most importantly: It starts at the top.
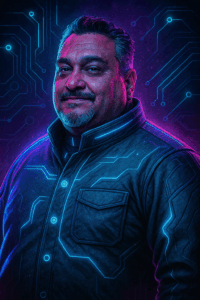
Meet the expert Sr. CyberSecurity Analyst Security Operations Center What he does: AllConnected’s Senior Cybersecurity Analyst (SCA), leads our Security Operations Center (SOC) and the

This month, National Preparedness Month encourages individuals and organizations to build a lasting legacy by protecting what you’ve built. Taking the first steps to becoming prepared for disaster. If you haven’t already, take that time to re-examine and strengthen the cybersecurity strategies at your organization.

Starting a new hire off right isn’t just about orientation… It’s about protecting your organization from day one. This webinar dives into the critical intersection of HR and IT, offering practical strategies to reduce risk, streamline onboarding, and build a secure foundation for your workforce.
As businesses grow, so do the complexities of managing operations, compliance, and employee needs. For many organizations, the key to scaling successfully isn’t doing more—it’s doing what matters most and finding trusted partners to handle the rest.