NIST Cybersecurity Framework is a set of standards, guidelines and practices for mitigating your organization’s cybersecurity risks, published by the US National Institute of Standards and Technology.
Back in 2013, Executive Order (EO) 13636 directed the executive branch of the United States to do the following:
This order was supported by the Cybersecurity Enhancement Act of 2014, and the National Institute of Standards and Technology (NIST) developed the aforementioned framework with the intention to reduce cyber risks to critical infrastructure.
Now, it is recommended that any organization — but particularly those which handle sensitive information that needs to be properly protected against cyber criminals — remain compliant with the latest NIST 800-171 mandate. If your organization works with the government at any capacity, compliance is mandatory.
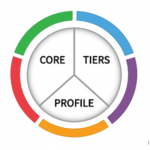
The Cybersecurity Framework consists of three main components: Implementation Tiers, the Framework Core, and your Company Profile:
The Tiers range from informal, reactive responses to more agile and risk-informed:
The Tiers you select should describe how well integrated your cybersecurity practice is with your organization’s broader risk decisions. That is, make sure that your Tier meets your organizational goals, reduces cybersecurity risk to acceptable levels, and can be consistently implemented.
![]()
Categories
The Categories were designed to cover the breadth of cybersecurity objectives for an organization, and include the physical environment, cyber security, employee training and communication, along with a focus on business outcomes.

Subcategories
At the deepest level, the Framework Core subcategories are 108 outcome-driven general statements. Use the following to determine how to create or improve your cyber security policies and practices based on your organization’s needs.
You can download the framework here.
Profiles can be used to identify opportunities for improving your organization’s cybersecurity strategy by comparing your “Current” Profile with a “Target” Profile.
To develop your Company Profile, after reviewing all of the Categories and Subcategories (download above):
Your Current Profile can then be used to prioritize and measure your progress toward the Target Profile, while factoring in other business needs, such as cost-effectiveness and innovation.
Profiles can be used to conduct self-assessments and communicate within an organization or between organizations.
Any non-compliance of the NIST 800-171 mandate can lead to potentially devastating consequences, regardless of your industry.
What different contracts does your organization hold? What are the individual compliance regulations for each? What kind of clients do you work with, and what kind of data are you collecting, storing, and using that needs to be kept secure? To get started on your cybersecurity framework, you need to start by thinking about all these questions.
There are so many components to building a NIST-based cybersecurity framework, and the only way to make sure you don't miss a step is to outline where your organization fits into the NIST guide. This is a complicated process in itself, and most organizations would benefit from partnering with an IT partner to create this or at least getting a consultation.
You already have plenty of business to handle, and the last thing you need to worry about is an additional area of risk arising from not having the proper technology, capabilities, and expertise at your disposal when it comes to maintaining compliance. Whether you're a small business with no dedicated IT department or a larger establishment with existing IT, partnering with the right MSP can give you peace of mind knowing you're doing everything you should be to maintain compliance. That is, assuming you pick the right IT partner...